Meet SOX Compliance Requirements
The Sarbanes-Oxley (SOX) Act requires corporate financial disclosure for all public companies in the US. Enacted in 2002, it is meant to strengthen corporate responsibility and prevent corporate and accounting fraud.
Ensuring Transparency of Corporate Financial Operations
Accurate and Verifiable Corporate Disclosures
The Sarbanes-Oxley Act of 2002 (SOX) is a federal law that sets a list of requirements for all U.S. publicly traded company boards, management, and public accounting firms. The purpose of the legislation is to improve the accuracy and reliability of corporate disclosures.
Executive Responsibility, Corporate Audits
Sections 302 (“Corporate responsibility for financial reports”) and 404 (“Management assessment of internal controls”) are of particular interest to information professionals. 302 holds CEO and CFOs personally responsible for disclosure accuracy, while 404 requires corporations to have their internal controls audited and reported annually to the SEC.
Examples of Addressed SOX Compliance Requirements
The Information Technology Governance Institute (ITGI) has used COSO and COBIT frameworks to create a set of specific IT control objectives for SOX. The requirements below are an example of COSO / COBIT recommendations that apply to Cygna Auditor.
AI3.2:
Infrastructure Resource Protection and Availability
AI7.7:
Final Acceptance Test
DS4.3:
Critical IT Resources
DS5.5:
Security Testing, Surveillance and Monitoring
DS10.2:
Problem Tracking and Resolution
AI6.5:
Change Closure and Documentation
DS3.5:
Monitoring and Reporting
DS5.3:
Identity Management
DS5.4:
User Account Management
DS13.3:
IT Infrastructure Monitoring
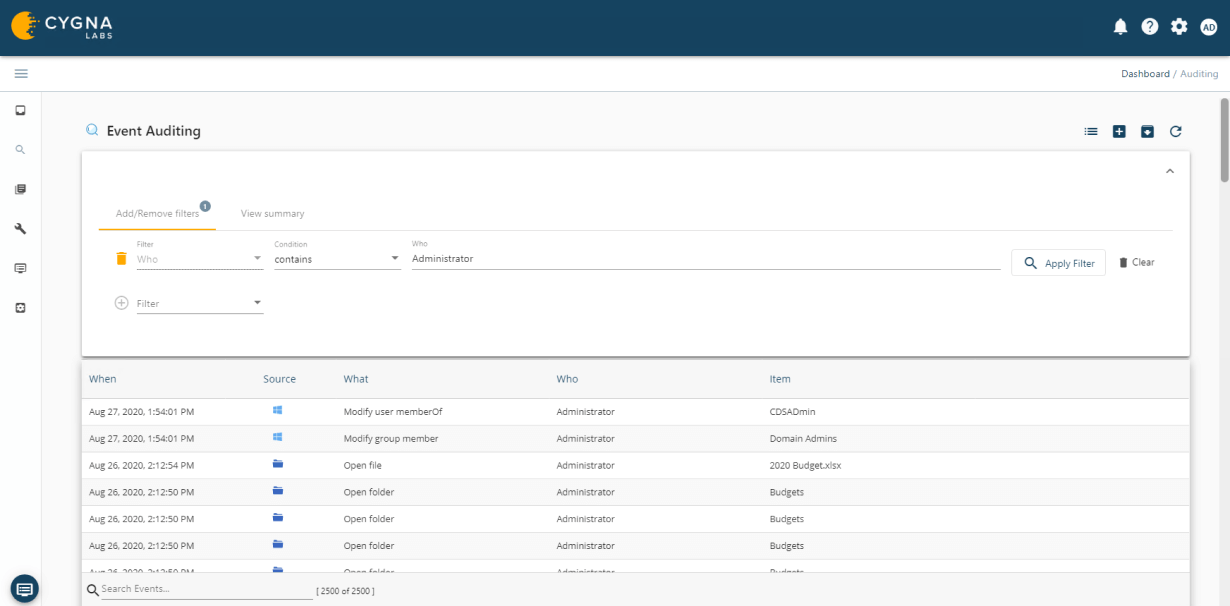
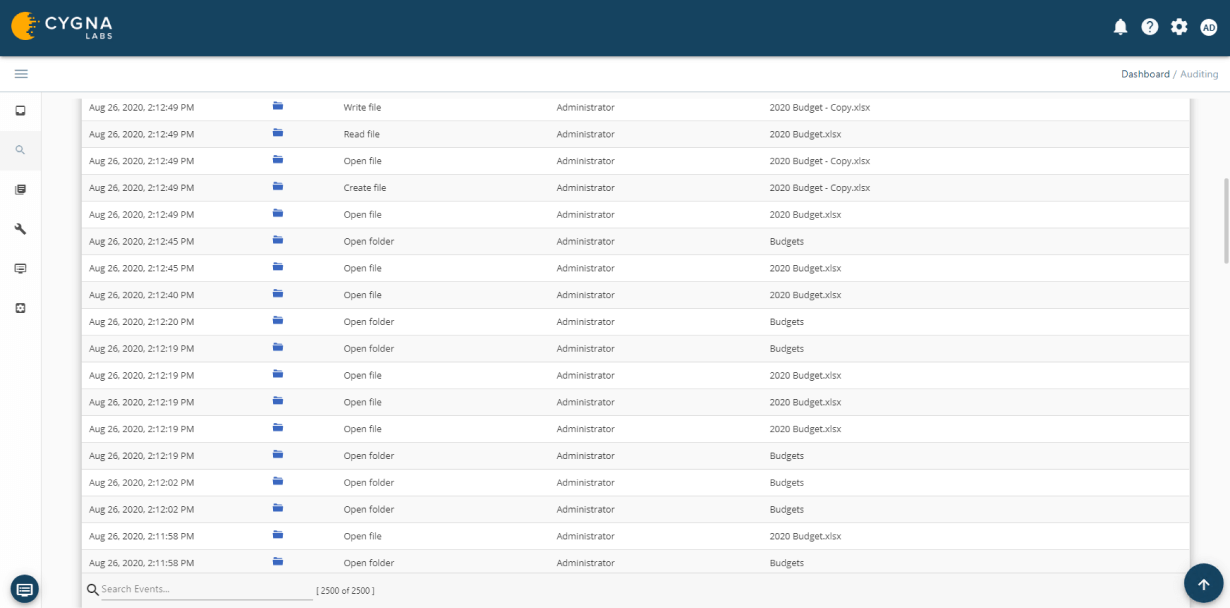
Monitor Activity on Secured Systems
Cygna Auditor monitors all successful and failed data activity such as file or folder creation, access, updates, deletions, who made the changes and when they were made.
Real-Time Notification of Sensitive Changes
Cygna Auditor's built-in and custom alerting notifies you of critical changes such as membership changes to privileged groups.
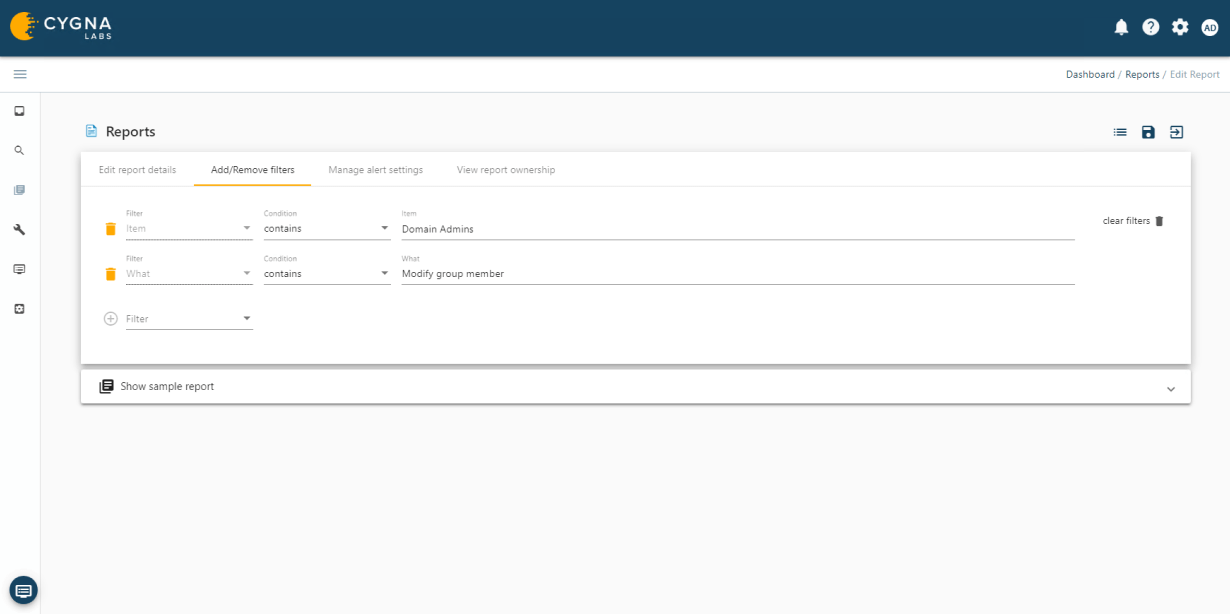
Privileged Account Management
Cygna Auditor allows you to monitor all changes made by privileged accounts to ensure they adhere to regulatory and organizational policies for the protection and privacy of data as well as that they do not abuse their unrestricted access.