ISO 27001 COMPLIANCE
ISO/IEC 27001 is an international standard for practices surrounding the management of an information security management system (ISMS). Certification requires maintaining of a high level information security and implementing the outlined best practices to manage and prevent IT-related risks.
ISO/IEC 27001:2013 is an information security standard that was published in September 2013. Unlike many other regulatory frameworks, it is a voluntary standard. As ISO is an international body, any organization in the world can adopt 27001. Those that choose to implement it can be formally audited to prove compliance to the standard.
ISO 27001 defines an Information Security Management System (ISMS) and how to design, deploy, and maintain such a system. It has over 100 controls over 14 security control sections. ISO 27001:2013 is an update of the original 2005 release that aligns better with management standards such as ISO 9000 and ISO/IEC 20000.
Most of the controls specified in ISO 27001 and applicable to Cygna Auditor are similar or identical to the controls specified in NIST Special Publication 800-53, the security control framework for the Federal Information Security Management Act of 2002 (FISMA) and a superset of the ISO 27001 controls. Appendix H of NIST 800-53 provides a mapping of ISO 27001 to NIST 800-53 controls; what follows is a sampling of controls that Cygna Auditor satisfies.
Organization of (internal) Information Security
System acquisition, development and maintenance
Human Resource Security
Supplier Relationships
Access Control
Information security incident management
Operations Security
Information security aspects of business continuity management
Communications Security
Compliance
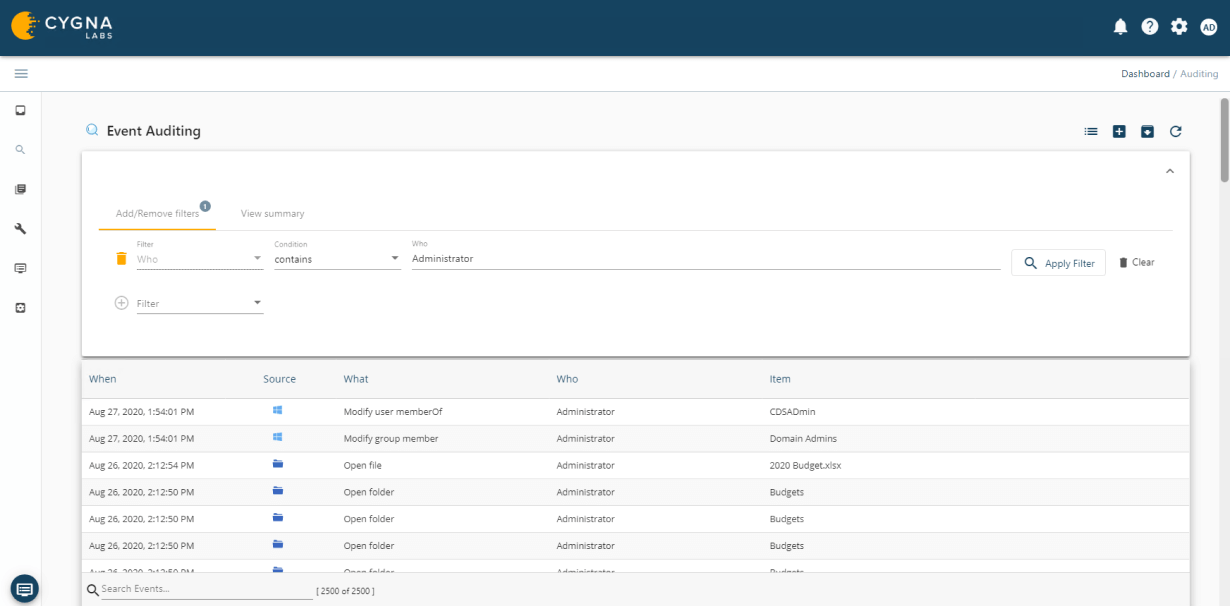
Cygna Auditor monitors all successful and failed data activity such as file or folder creation, access, updates, deletions, who made the changes and when they were made.

Cygna Auditor's built-in and custom alerting notifies you of critical changes such as membership changes to privileged groups.
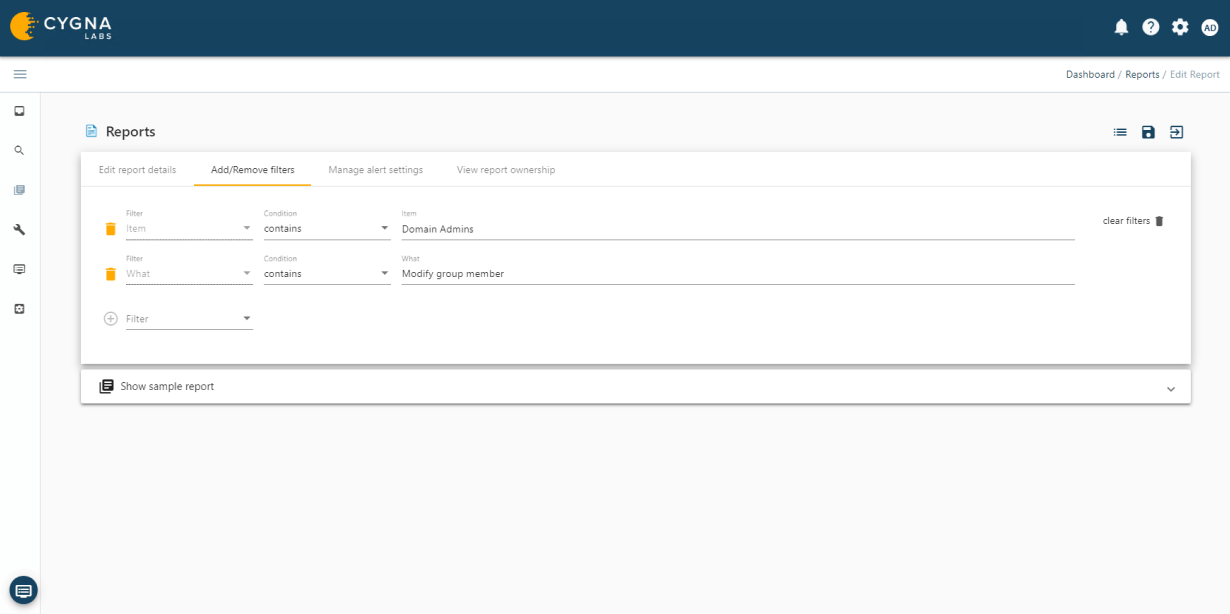
Cygna Auditor allows you to monitor all changes made by privileged accounts to ensure they adhere to regulatory and organizational policies for the protection and privacy of data as well as that they do not abuse their unrestricted access.
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.