
GLBA COMPLIANCE
Achieve GLBA Compliance with Advanced Security Solutions
The Gramm-Leach-Bliley Act (GLBA) requires all financial institutions in the United States to implement appropriate security controls that ensure the confidentiality of customer information, protect against unauthorized access, and mitigate potential threats.
Protecting Personal Financial Data of US Citizens
GLBA enables large financial services organization flexibility
The Gramm-Leach-Bliley Act (GLBA) modernized the US financial system by removing barriers that previously prevented financial services organizations from operating as investment banks, commercial banks, and insurance companies simultaneously.

Mandatory personal data requirements
As a result of the increased risks to personal data posed by large financial mergers, GLBA established three key requirements for data protection: the Financial Privacy Rule, the Safeguards Rule, and the Pretexting Protection. These requirements are mandatory for all US financial institutions.

Addressed GLBA Compliance Requirements
Cygna Auditor addresses topics in the FFIEC IT Examination Handbook, which includes both Tier I and Tier II Objectives and Procedures. Note that the list below is not exhaustive, but only a sample of requirements that Cygna Auditor can address.
Objectives 2(4), 2 (6), 6 (3)
Procedures / A (Authentication and Access Controls): Authentication (2), (4), (7)
Procedures / C (Host Security): (7), (9)
Procedures / G (Application Security): (1), (3), (7)
Procedures / M (Security Monitoring): (1), (2), (5), (6), (7), (8), (9), (14), (18), (22)
Procedures / A (Authentication and Access Controls): Access Rights Administration (1), (2), (4), (5), (6), (7)
Procedures / B (Network Security): (8), (12), (19)
Procedures / D (User Equipment Security): (3), (6)
Procedures / L (Data Security): (2), (3)
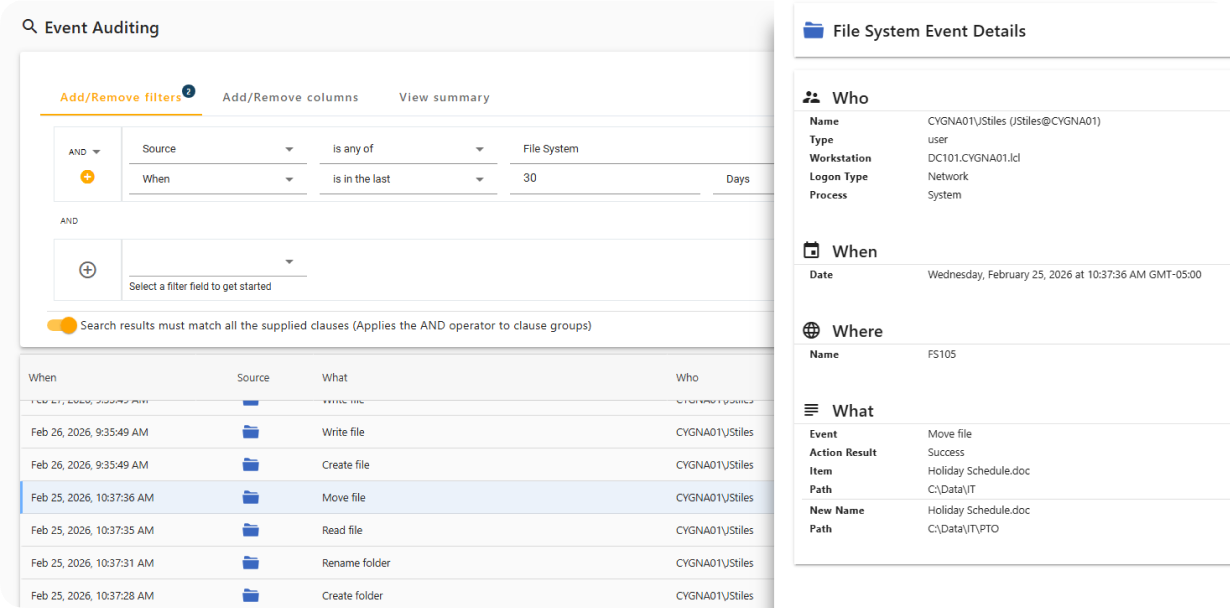
Monitor Activity on Secured Systems
Cygna Auditor captures both successful and failed data access events, including file and folder creation, access, updates, and deletions, while providing full attribution of who performed each action and when.
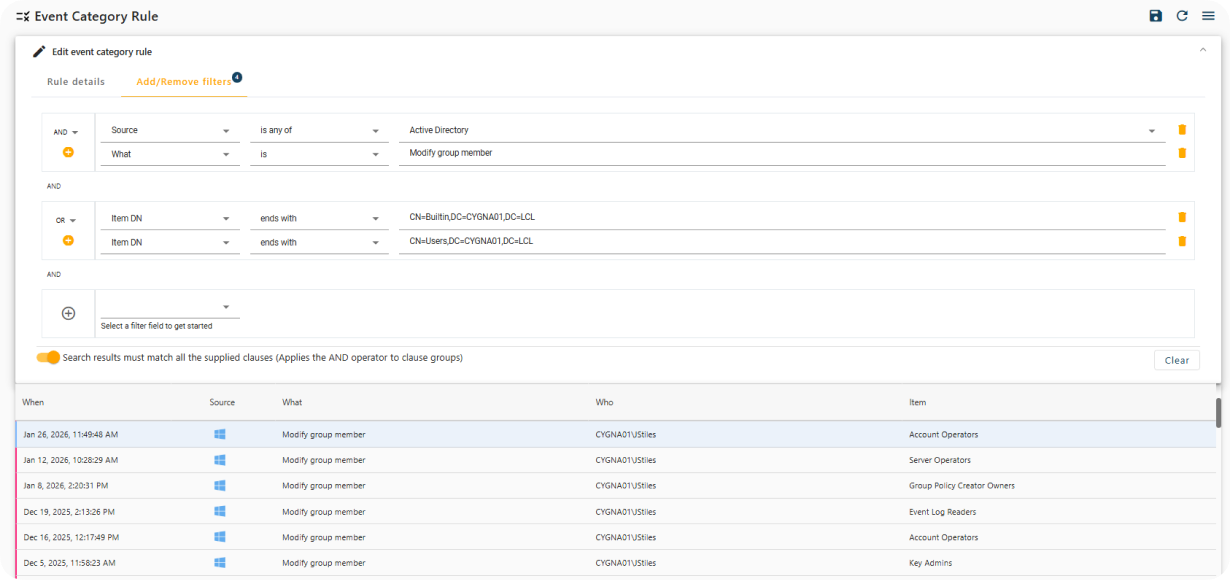
Real-Time Notification of Sensitive Changes
Cygna Auditor provides built-in and customizable alerts that immediately notify you of critical security events, such as changes to privileged group membership.
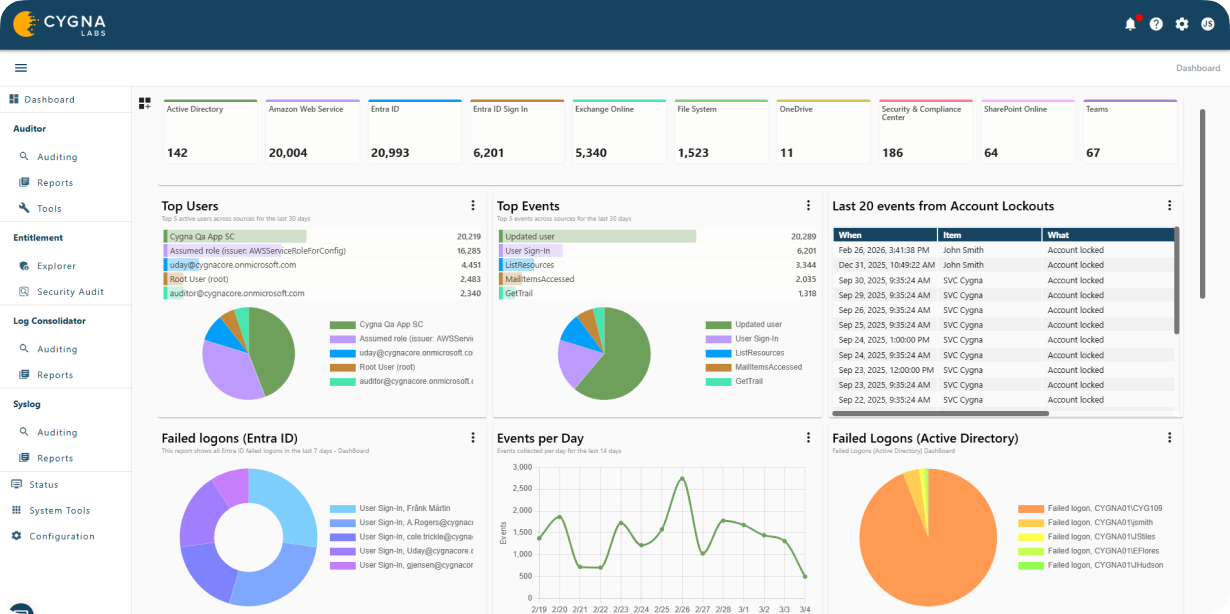
Privileged Identity Activity Visualization
Cygna Auditor monitors all changes made by privileged identities to ensure compliance with regulatory and organizational policies and to prevent misuse of elevated access.

Meet GLBA Compliance Requirements
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.
