FISMA COMPLIANCE
Achieve FISMA Compliance with Advanced Security Solutions
The Federal Information Security Management Act (FISMA) establishes a framework for protecting federal information systems through effective security controls. All U.S. federal agencies and contractors must meet the minimum security requirements outlined in FIPS 200.

Strengthening Information Security of Federal Agencies Through FISMA Compliance
All federal agencies must meet FISMA security mandate
The Federal Information Security Management Act of 2002 (FISMA) is a foundational law for federal information security in the United States. It requires all U.S. federal agencies to develop, document, and implement an information security program to protect agency systems and data.

NIST-developed security controls underpin FISMA
Under FISMA, the National Institute of Standards and Technology (NIST) develops the security standards and guidelines Federal agencies must follow. FIPS 200 establishes the minimum security requirements for Federal systems while NIST SP800-53 provides a complimentary list of recommended security controls.

Addressed FISMA Compliance Requirements
Cygna Auditor addresses many of the controls outlined in NIST Special Publication 800-53 Revision 4, Security and Privacy Controls for Federal Information Systems and Organizations. The list below is not exhaustive, but represents a sample of the requirements Cygna Auditor can address.
Access Control:
Security Assessment and Authorization:
Contingency Planning:
Incident Response:
Media Protection:
Audit and Accountability:
Configuration Management:
Identification and Authentication:
Maintenance:
System and Information Integrity:
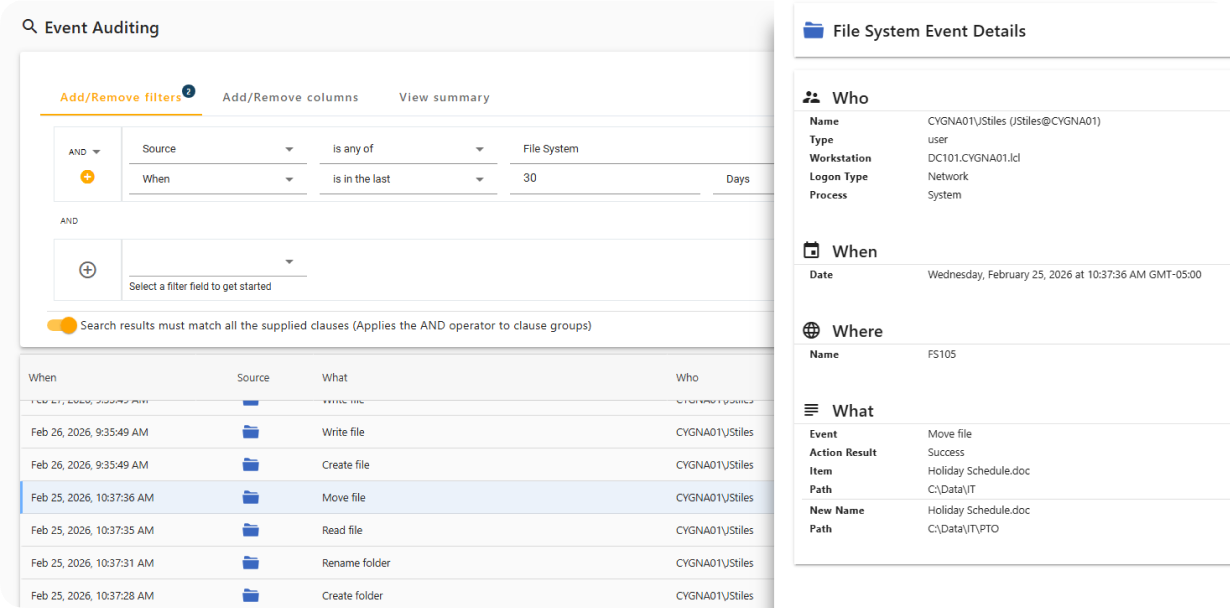
Monitor Activity on Secured Systems
Cygna Auditor captures both successful and failed data access events, including file and folder creation, access, updates, and deletions, while providing full attribution of who performed each action and when.
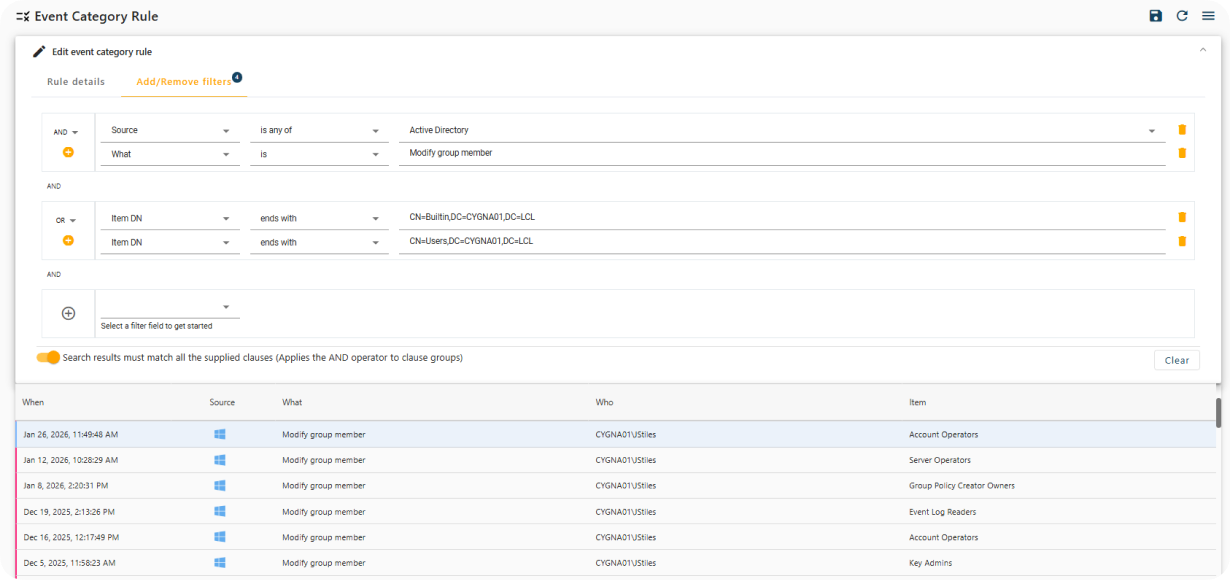
Real-Time Notification of Sensitive Changes
Cygna Auditor provides built-in and customizable alerts that immediately notify you of critical security events, such as changes to privileged group membership.
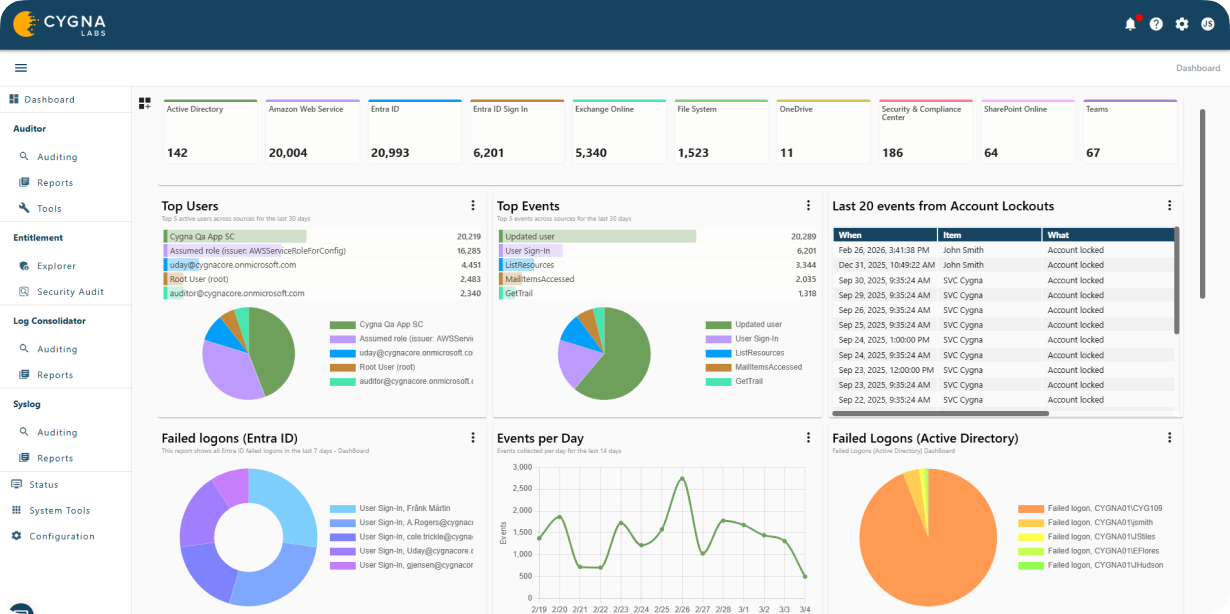
Privileged Identity Activity Visualization
Cygna Auditor monitors all changes made by privileged identities to ensure compliance with regulatory and organizational policies and to prevent misuse of elevated access.
Meet FISMA Compliance Requirements
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.

