GOVERNMENT
Securing Government Data and Compliance with Advanced IT Solutions
Protect sensitive government data and maintain compliance with evolving regulations

Meet the demands of government compliance with confidence
Exceed auditors' expectations
Demonstrate compliance by giving auditors the detailed records they need during reviews. Accurate reporting provides transparency and supports adherence to regulatory standards.

Real-time alerts
Receive notifications of critical changes to your environment so you can take action right away. Real-time alerts allow agencies to respond quickly and maintain compliance with regulatory requirements.

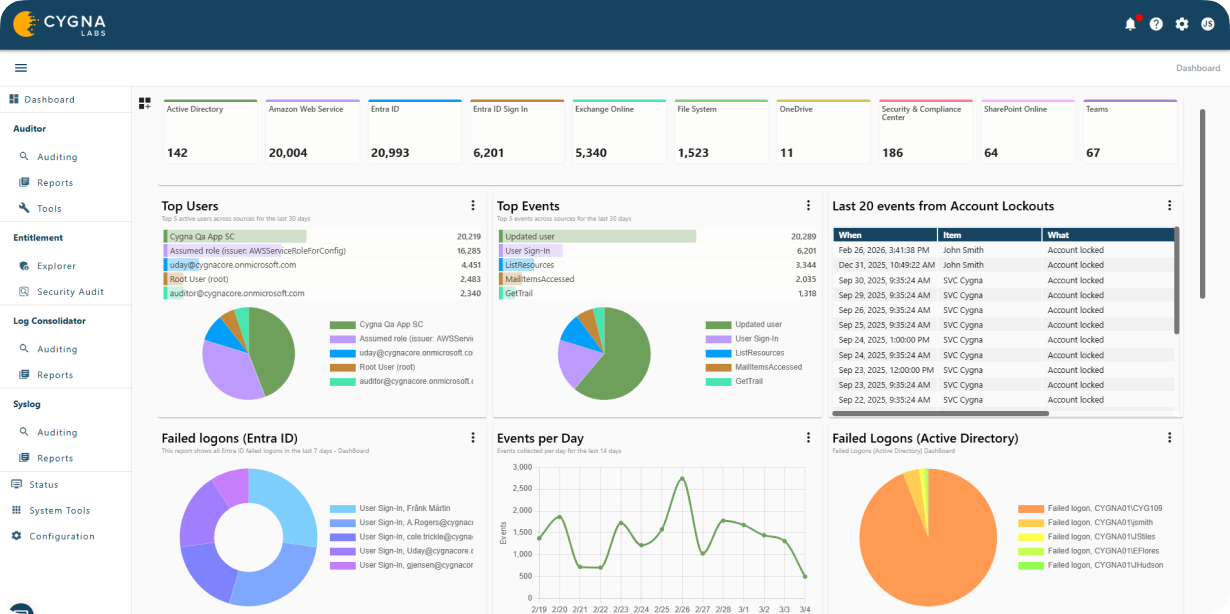
Consolidated web console
Organizations require a simple way to view all of their compliance data that spans across both on premises and in the cloud all within a single solution and screen. This unified view helps agencies oversee activity and maintain compliance consistently.

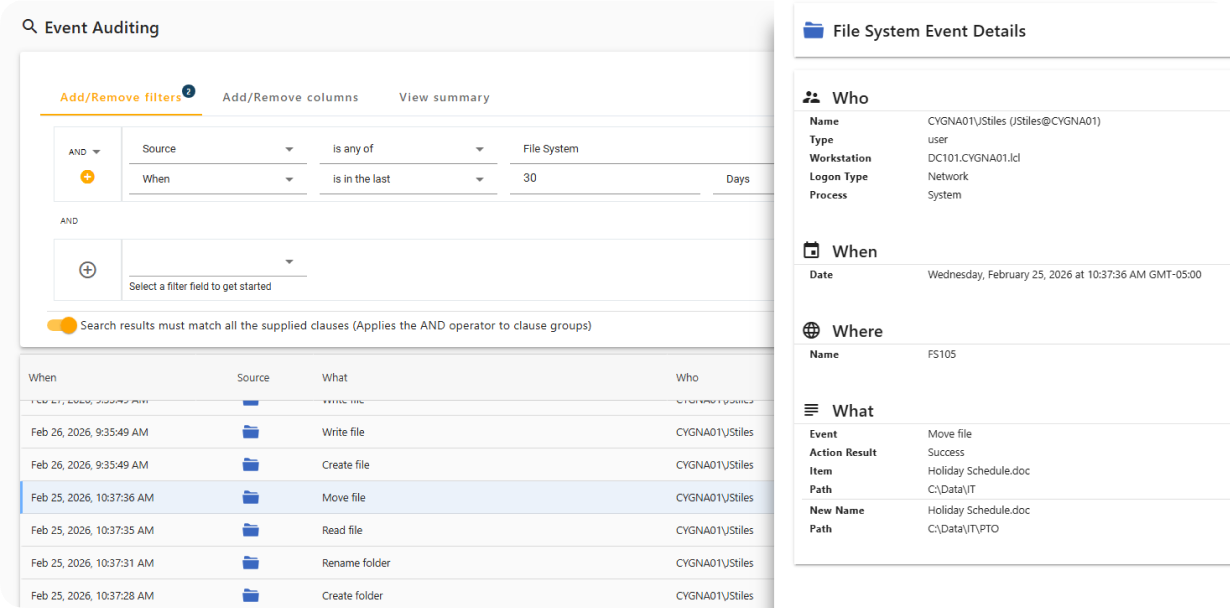
Monitor Activity on Secured Systems
Cygna Auditor captures both successful and failed data access events, including file and folder creation, access, updates, and deletions, while providing full attribution of who performed each action and when.
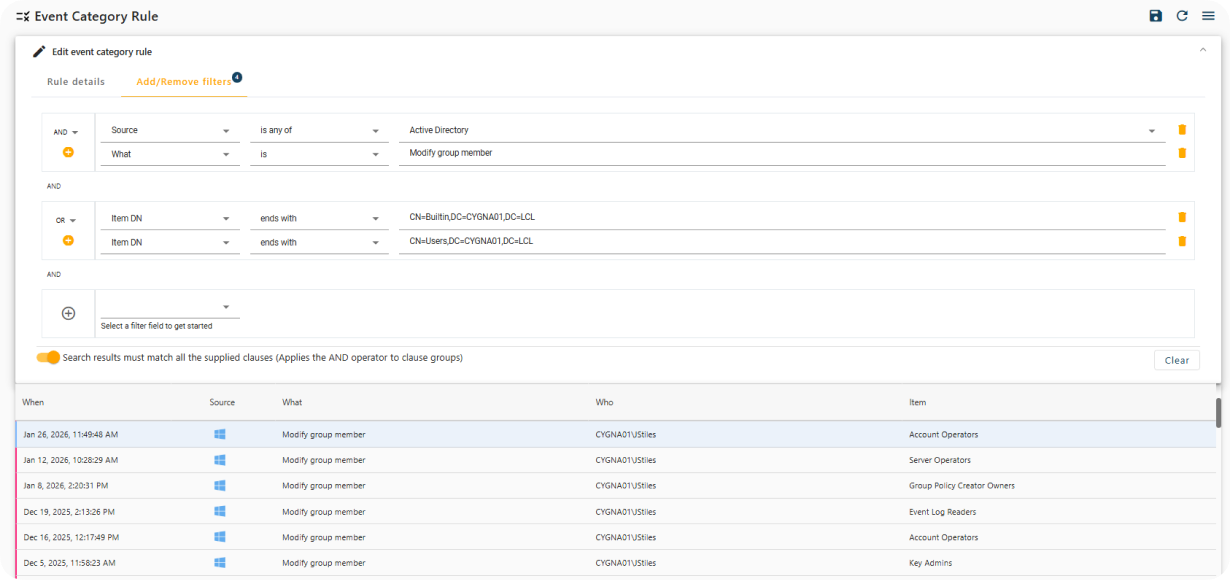
Real-Time Notification of Sensitive Changes
Cygna Auditor provides built-in and customizable alerts that immediately notify you of critical security events, such as changes to privileged group membership.
Privileged Identity Activity Visualization
Cygna Auditor monitors all changes made by privileged identities to ensure compliance with regulatory and organizational policies and to prevent misuse of elevated access.
Cygna Auditor helps organizations prove compliance for government regulations
FISMA/NIST compliance
The Federal Information Security Management Act (FISMA) defines a framework for ensuring the effectiveness of security controls across federal information systems. It is supported by NIST standards, which provide detailed guidelines for risk management, continuous monitoring, and security assessment.

Requiring data protection for all organizations
The General Data Protection Regulation (GDPR) strengthens and unifies data protection for individuals across the European Union. It also applies to non-EU companies that handle EU citizens’ personal data. Other jurisdictions are implementing similar regulations to safeguard personal information.

PCI DSS compliance
The Payment Card Industry Data Security Standard (PCI DSS) is designed to protect cardholder data by requiring organizations to maintain secure systems and processes. Compliance involves controls such as encryption, network monitoring, and regular security testing to prevent unauthorized access to payment information.

Protect sensitive citizen data while simplifying regulatory compliance with Cygna Auditor
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.

