ISO 27001 Compliance
Strengthen Information Security with ISO 27001 Compliance Solutions
ISO/IEC 27001 is an international standard for managing information security through an Information Security Management System (ISMS). Certification requires maintaining a high level of information security and implementing best practices to manage and prevent IT-related risks.

The International Standard for Information Security Management Systems
Voluntary, auditable, and certifiable
ISO/IEC 27001 defines an Information Security Management System (ISMS) that outlines how to design, implement, and maintain a comprehensive information security program. It includes 93 controls organized across 4 domains (Organizational, People, Physical and Technological). Unlike many regulatory frameworks, it is voluntary. Because ISO is an international body, any organization worldwide can adopt ISO 27001. Those that choose to implement it can be formally audited to demonstrate compliance with the standard. Cygna Labs is proud to hold an ISO 27001 certification.

NIST-aligned security controls reinforce ISO 27001
ISO 27001:2022 was updated in 2022 and has replaced the older ISO 27001:2013 version. This update addresses modern issues of cloud adoption, remote work and evolving cyber threats. Further, the updated framework has been more closely aligned to other risk-based frameworks such as GDPR and NIST.

Addressed ISO 27001 Compliance Requirements
Most of the controls specified in ISO 27001 and addressed by Cygna Auditor are similar or identical to those in NIST Special Publication 800-53, the security control framework supporting the Federal Information Security Management Act (FISMA) of 2002. NIST SP 800-53 serves as a superset of ISO 27001 controls, with Appendix H providing a detailed cross-reference between the two. The list below highlights a sample of controls that Cygna Auditor satisfies.
Organization of (internal) Information Security:
Human Resource Security:
Access Control:
Operations Security:
Communications Security:
System acquisition, development and maintenance:
Supplier Relationships:
Information security incident management:
Information security aspects of business continuity management:
Compliance:
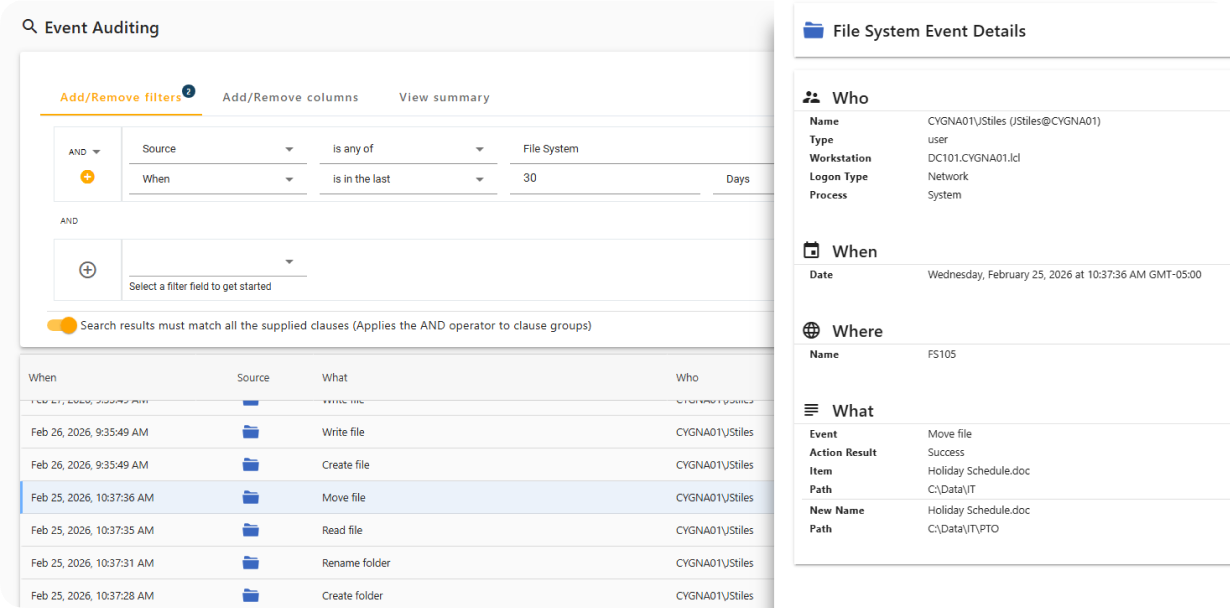
Monitor Activity on Secured Systems
Cygna Auditor captures both successful and failed data access events, including file and folder creation, access, updates, and deletions, while providing full attribution of who performed each action and when.
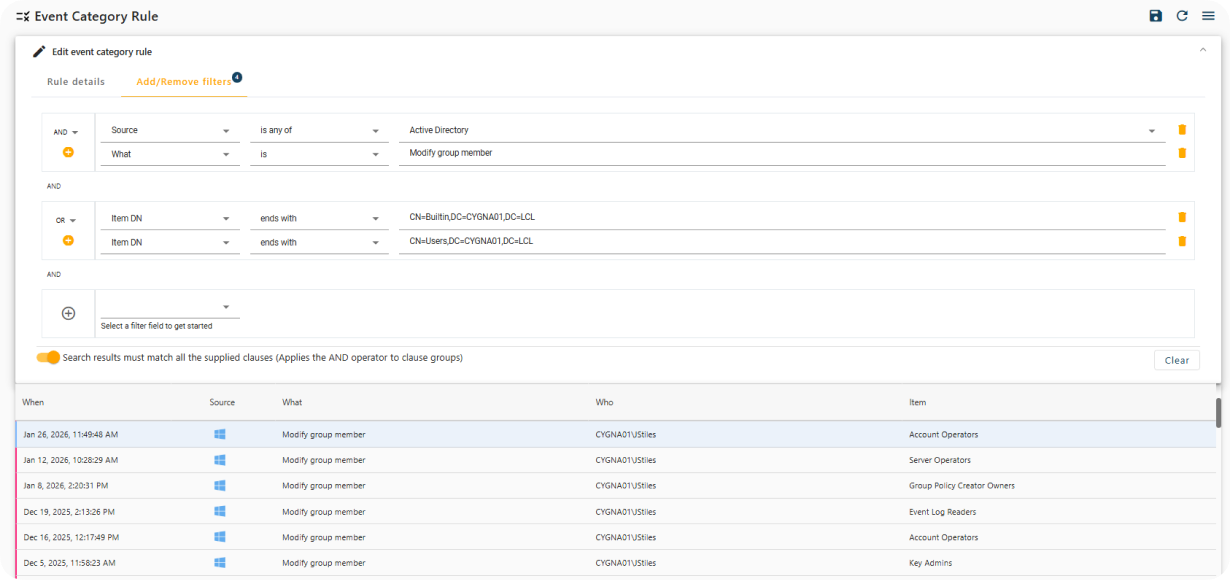
Real-Time Notification of Sensitive Changes
Cygna Auditor provides built-in and customizable alerts that immediately notify you of critical security events, such as changes to privileged group membership.
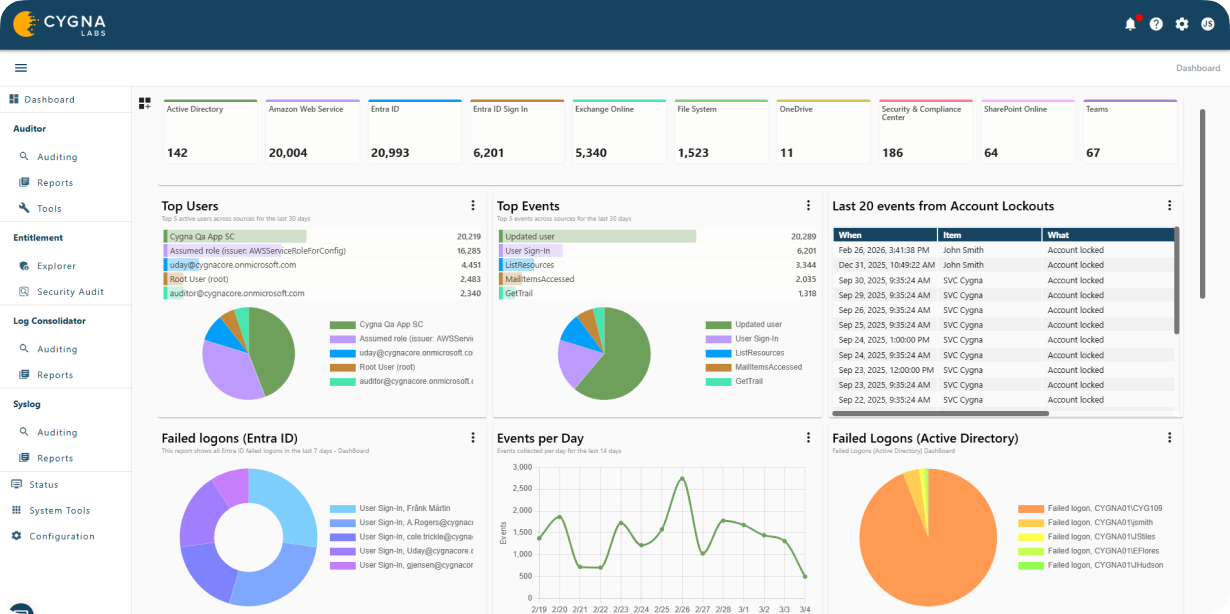
Privileged Identity Activity Visualization
Cygna Auditor monitors all changes made by privileged identities to ensure compliance with regulatory and organizational policies and to prevent misuse of elevated access.
Meet ISO 27001 Compliance Requirements
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.

