PCI COMPLIANCE
Achieve PCI Compliance with Robust Security Solutions
PCI DSS standards ensure the security of credit card transactions by requiring organizations to implement a combination of relevant policies, procedures, and technical measures to protect cardholder data

Implementing Information Security Controls for Credit Card Processors
Industry defined requirements
The Payment Card Industry Data Security Standard (PCI DSS) is a set of minimum requirements established by the PCI Security Standard Council that any business that processes payment cards (e.g. credit or debit cards) must meet in order to secure the data to protect the cardholder.

Security standards to protect cardholder data
The aim of the standard is to enforce a set of carefully checked security guidelines. These policies are designed to prevent the compromise of customers' financial data held by merchants or service providers and obtained as part of payment card transactions.

Addressed PCI Compliance Requirements
Cygna Auditor addresses PCI DSS Requirement 7 (restrict access to cardholder data by business need to know) and Requirement 10 (track and monitor all access to network resources and cardholder data). See the list below for the control IDs covered.
Limit access to system components and cardholder data to only those individuals whose job requires such access
Implement automated assessment trails for all individual user accesses to cardholder data
Implement automated assessment trails for all actions taken by any individual with root or administrative privileges
Implement automated assessment trails for access to all audit trails
Implement automated assessment trails for invalid Logical Access attempts
Implement automated assessment trails for use of and changes to identification and authentication mechanisms and all changes, additions, or deletions to accounts with root or administrative privileges
Implement automated assessment trails for initialization of Assessment Logs
Implement automated assessment trails for Creation and Deletion of System Level Objects
Record at least User Identification, Type of Event, Date and Time, Success or Failure Indication, Origination of Event, and Identity or name of effected data, system component, or resource
Review logs and security events for all system components to identify anomalies or suspicious activity
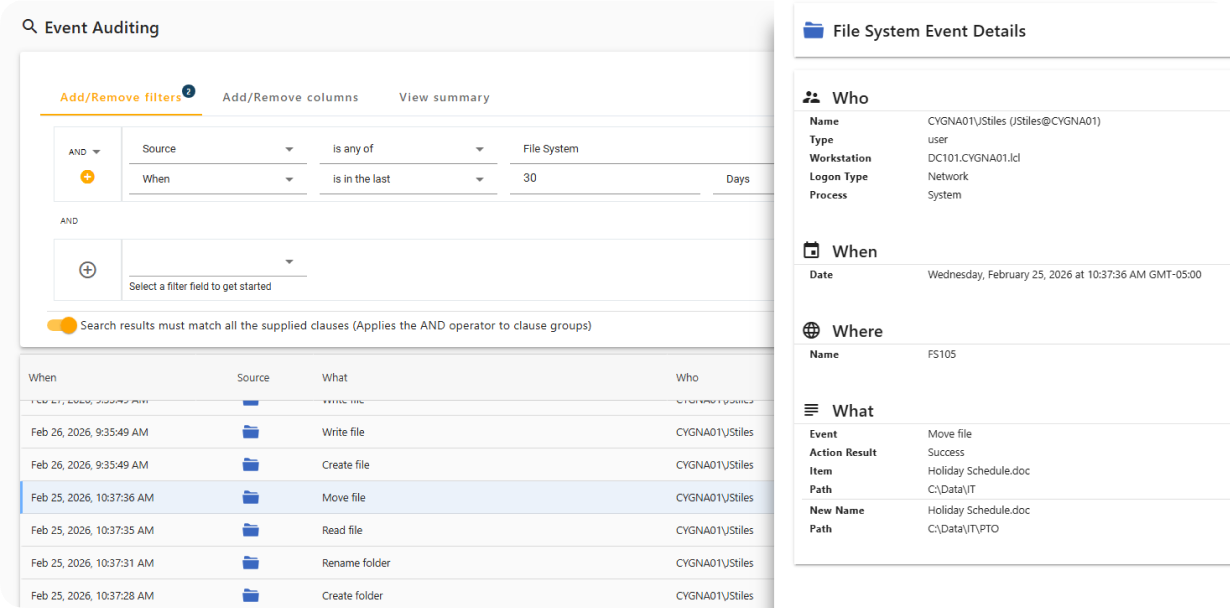
Monitor Activity on Secured Systems
Cygna Auditor captures both successful and failed data access events, including file and folder creation, access, updates, and deletions, while providing full attribution of who performed each action and when.
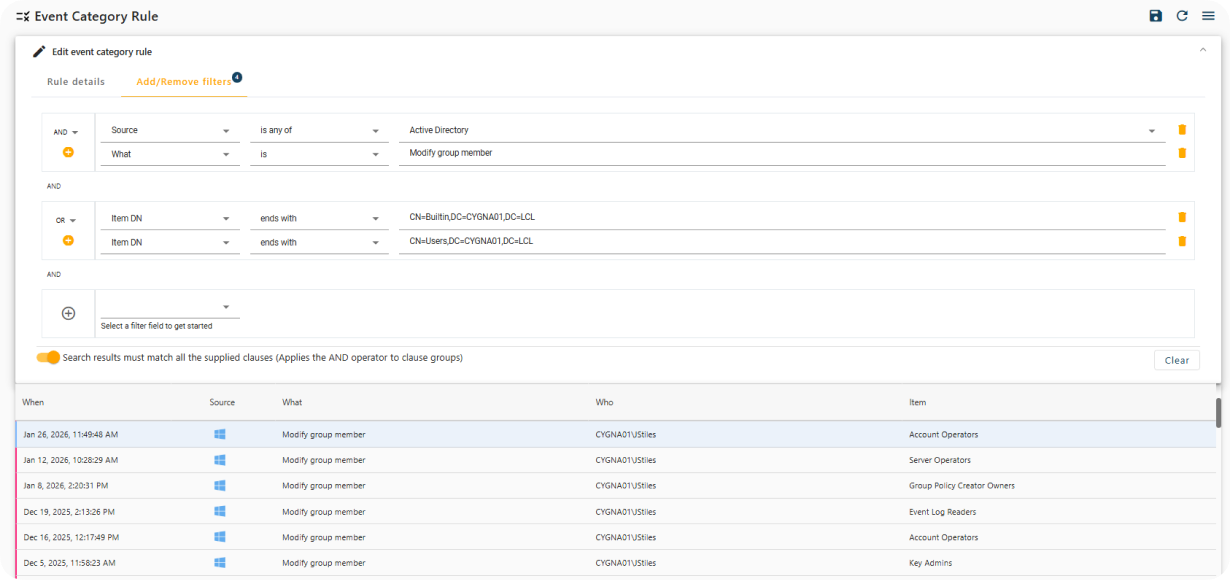
Real-Time Notification of Sensitive Changes
Cygna Auditor provides built-in and customizable alerts that immediately notify you of critical security events, such as changes to privileged group membership.
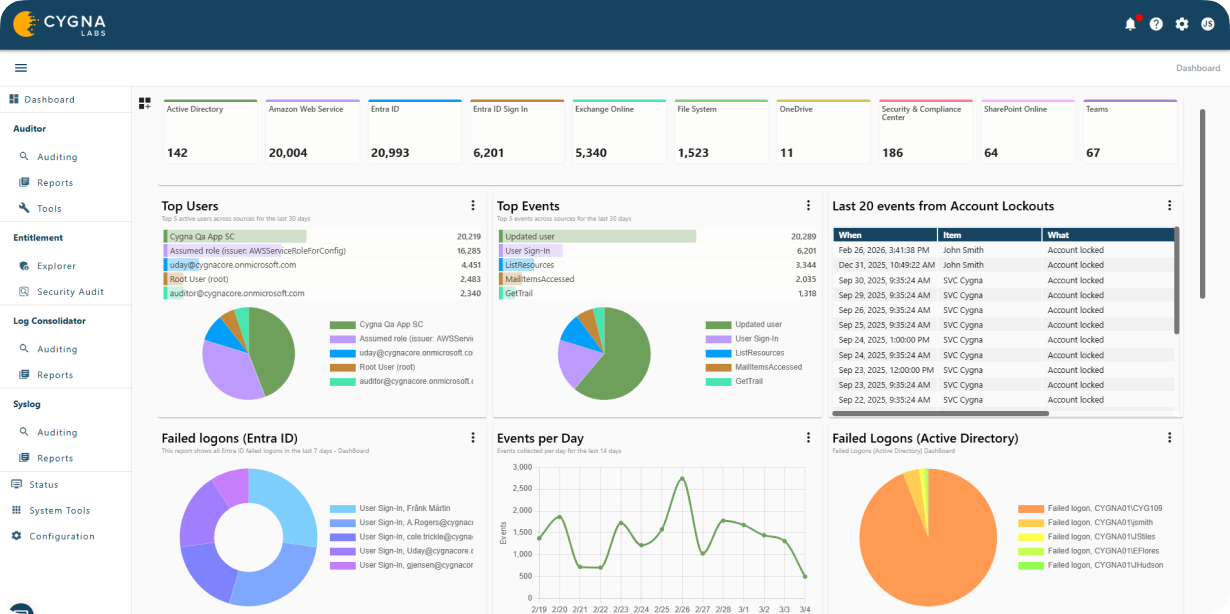
Privileged Identity Activity Visualization
Cygna Auditor monitors all changes made by privileged identities to ensure compliance with regulatory and organizational policies and to prevent misuse of elevated access.
Meet PCI Compliance Requirements
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.

