
N3K wird zu Cygna Labs Deutschland
Moderne Netzwerke erfordern Flexibilität, Widerstandsfähigkeit und Sicherheit. Angesichts der zunehmenden Cloud-Nutzung und der sich entwickelnden Bedrohungen benötigen IT-Teams eine Lösung, die für die Skalierung ausgelegt ist. Unser QIP DHCP-Server ist ein speziell entwickelter DHCP/DHCPv6-Server, der unübertroffene Zuverlässigkeit und Leistung bietet. VitalQIP automatisiert die DDI-Verwaltung, stärkt die Netzwerksicherheit und gewährleistet eine hohe Verfügbarkeit - für eine zuverlässige und zukunftssichere Infrastruktur.
Nutzen Sie unsere Managed Services zur Unterstützung Ihrer VitalQIP-DDI-Infrastruktur und/oder für Umzüge, Ergänzungen und Änderungen.
Umfassende IPv4- und IPv6-Adressplanung, -zuweisung und -vergabe mit integriertem Multi-Vendor-DHCP, DHCPv6 und DNS-Unterstützung.
Ergänzen Sie Ihre Netzwerk-Defense-in-Depth-Strategie um eine DDI-Ebene mit DNS-Sicherheit, IP-Adressen-Integrität sowie zentralem Reporting und Forensik.
Die REST-API, SOAP/XML-API und CLIs von VitalQIP erleichtern die Integration von Drittanbietern für eine optimierte IT-Automatisierung von DDI-Funktionen.
Erweitern Sie Ihre VitalQIP-Implementierung mit der Software DDI Guard, die sich nahtlos integrieren lässt, um eine detaillierte Übersicht und Archivierung von DHCP- und DNS-Transaktionen im Netzwerk zu ermöglichen. Analysen bieten Trendberichte, Dashboards und Analysen für IP-Adress- und DNS-Ressourcendatensatz-Rückforderungsfunktionen.
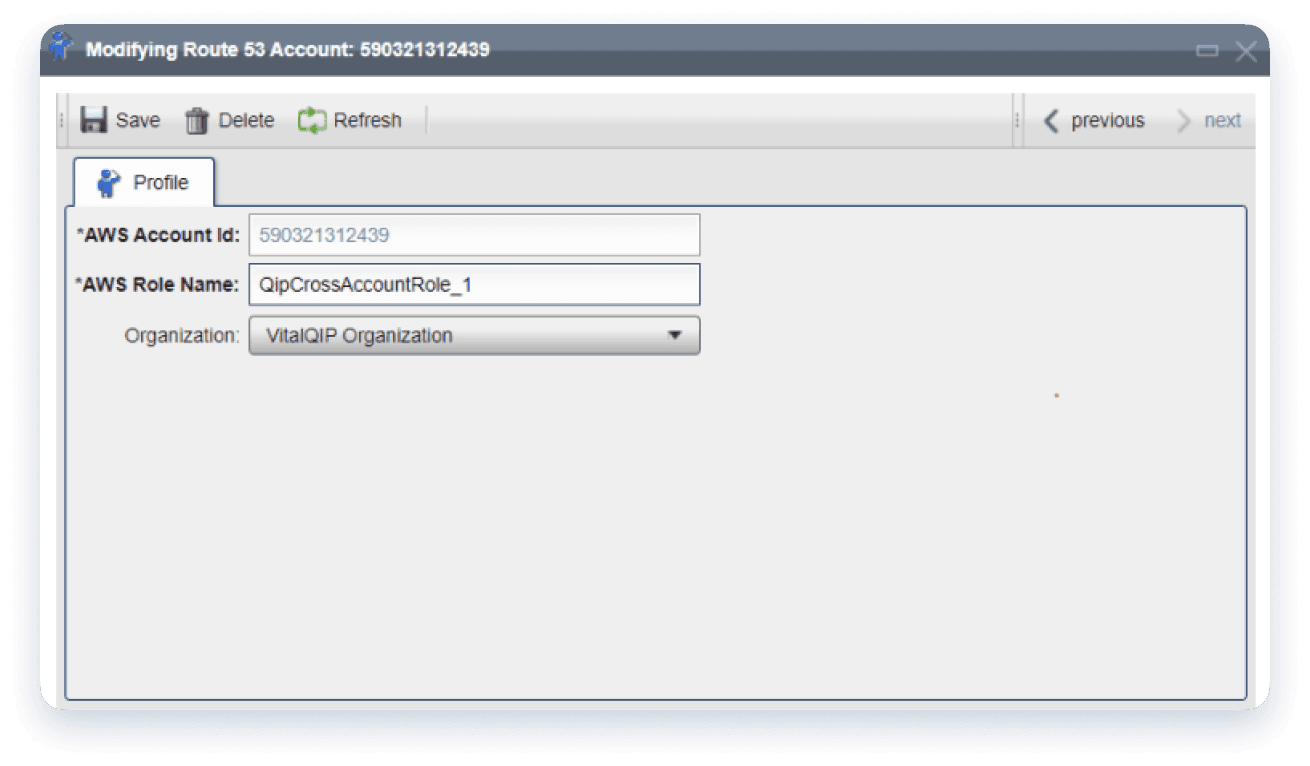
Verwalten Sie sowohl Ihre lokalen als auch Ihre Cloud-DNS-Dienste über eine einheitliche Benutzeroberfläche. VitalQIP bietet Unterstützung für Cloud-Zonen und Ressourceneinträge für Amazon Route 53 und Microsoft Azure DNS.
VitalQIP, eine weltweit führende IP-Verwaltungslösung, hat sich weiterentwickelt, um die DDI-Verwaltung für moderne Netzwerke zu erleichtern. VitalQIP ermöglicht die Verwaltung von Multi-Cloud-DNS-Diensten und die Verwaltung von IP-Adressen für Clouds, Rechenzentren und Remote-Standorte über Ihr WAN- oder SDWAN-Netzwerk.
Deployment
Im Gegensatz zu anderen Lösungen ermöglicht VitalQIP die zentralisierte Verwaltung von LAN/WAN und Multi-Cloud-DDI mit Software, Hardware und virtuellen Geräten, die jede Größenordnung bewältigen können.
Behalten Sie den Überblick in Ihrem Netzwerk
TRUSTED BY OVER 5,000 ORGANIZATIONS WORLDWIDE
Fortune-500-Unternehmen verlassen sich auf die Produkte und Dienstleistungen von Cygna Labs, um DDI zu verwalten, Datensicherheitsbedrohungen zu erkennen und proaktiv abzuschwächen, Compliance-Audits kostengünstig zu bestehen und die Produktivität ihrer IT-Abteilungen zu steigern.


SUCCESS STORY
„Da die Zahl der Geräte und Anwendungen kontinuierlich wächst, müssen die Provider Schritt halten, um in diesem Wettbewerb nicht irgendwann das Nachsehen zu haben. IP Control von Cygna Labs bietet uns die volle Kontrolle, mit der wir unsere IP-Adressen jetzt und auch langfristig verwalten können.“
SUCCESS STORY

„Cygna Diamond IP hat unsere Erwartungen definitiv erfüllt. Es ist sehr stabil und einfach zu bedienen, und wir verwenden es täglich, um IP-Adressen zu reservieren, neue Netzwerke zu erstellen und die APIs zur Automatisierung von Aufgaben zu nutzen.“
Erfahren Sie, welchen Mehrwert VitalQIP für Sie und Ihr Unternehmen bietet. Vereinbaren Sie einen auf Sie zugeschnittenen Kennenlerntermin und lassen Sie sich überzeugen, dass grundlegende DDI-Dienste einfach zu erreichen sind.