CYGNA SECURITY AND COMPLIANCE
M365 Cloud Auditing
Secure and monitor hybrid identity and infrastructure systems, including M365

Audit
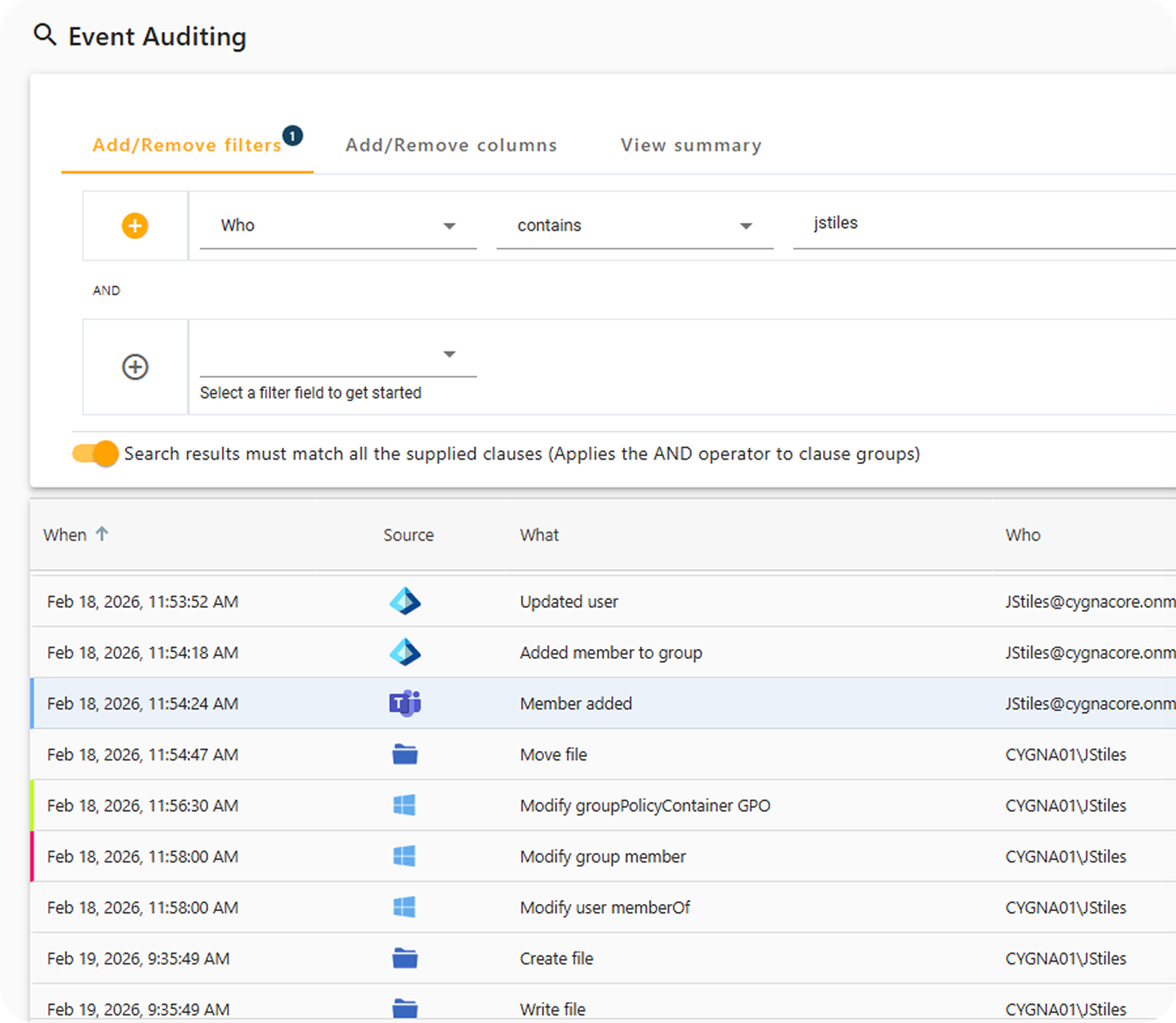
Track all changes and potential threats across multiple platforms including Active Directory, Entra ID, M365, Azure, Windows File Servers and AWS, all in the same console, in a single pane of glass. This allows easy Forensic Analysis across all platforms to easily determine the scope of a potential breach.
Easily build custom reports and minimize time and effort for compliance reporting with built in reports for PCI, SOX, HIPAA and FISMA.
Enable the new Risk Radar feature which leverages machine learning to find logons from unexpected locations or from unexpected hosts. Changes can be color coded for easy sorting and faster remediation of high-risk threats.
Enrich SIEM, SOAR and other SOC tools with detailed, real-time Active Directory threat detection.
Recovery
When you notice that an unauthorized or malicious change has taken place, you can immediately rollback those changes in both AD and Entra ID, all from a single console. Whether the change is something minor like a deletion of a user, OU or GPO or something more significant such as a large scale deletion or scripted change to attributes or groups.
Cygna offers Continous Recovery with instant rollback capabilities. This allows you to restore an object to a previous state in time, but without worrying about changes that took place after your last snapshot.
With Cygna’s granular rollback capabilities you don’t need to rollback all of the changes, just the ones you don’t want. This has proven key for clients that utilize scripted changes to hundreds or thousands of objects that may have correctly altered serval attributes, but mistakenly changed another.

Automated group membership remediation
The Desired State configuration feature constantly monitors specific groups within AD and Entra ID and issues an alert when those groups are modified. In addition, you can configure automated remediation of those groups when a membership change is detected, rolling back the changes to those groups in order to lower your security exposure and reduce your overall risk.

Let Us Help You Tackle Your IT Challenges
Schedule your demo today to see what's possible.
