CYGNA LOG CONSOLIDATOR
Log Aggregation
Management Tool for
Enhanced IT Management
Collection and centralized storage of Windows event log data for analysis.

Cygna Log Consolidator
Auditing Event Logs gives you crucial visibility into the health, performance, and security of your systems. These logs capture detailed information about authentication attempts, system errors, configuration changes, and application behavior, allowing you to identify and alert on anomalies early. By regularly reviewing them, you can detect warning signs before they escalate into outages or security incidents.
Centralized event
collection and storage
Log auditing supports compliance and forensic investigations. Many regulations require proof of proper monitoring and access control, which event logs help provide. In the event of a breach or operational failure, well-maintained logs give you the timeline and context needed to understand what happened, respond effectively, and prevent the issue from recurring. With user configurable reports, alerts and dashboards you can easily find specific events related to logons, event logs being cleared or other changes that have been made to local servers.
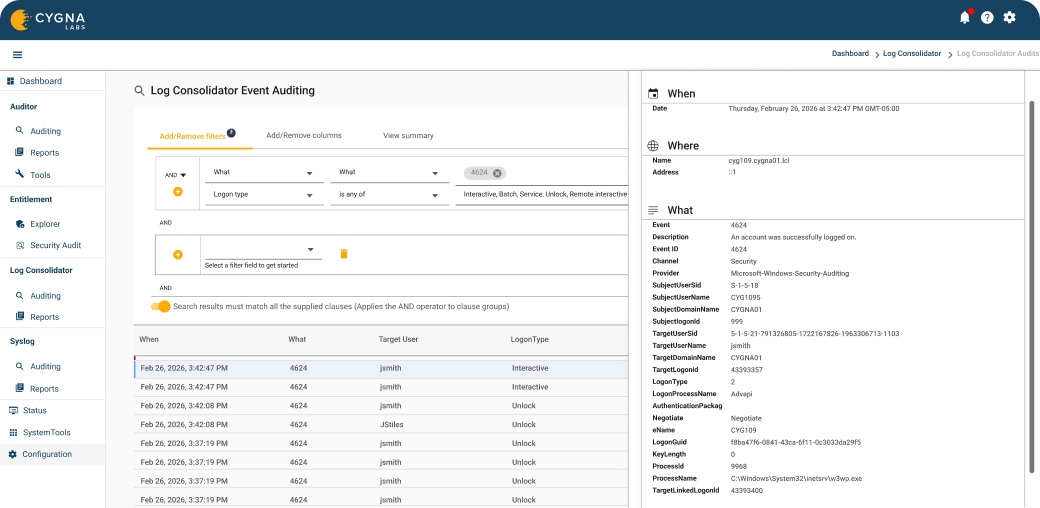

Centralized Web-Based Console
Simple to use web interface, no need for an additional client or an additional console to query and report on all of your Cygna Auditor data, from AD changes to Event logs.

Built-in and Customizable reports
Library of built-in event queries and reports to simplify the collection and reporting of events for operations, security and compliance.

Real-Time Alerts
Get notified in real-time of critical events that may require immediate attention. Alerts can be sent via email, Teams, webhooks or other systems.
Take control of your systems today
Take the first step towards insight, alerts, and compliance on your audit data. Learn more by downloading a Cygna Auditor datasheet.
Request a Demo
Our experienced engineers will fine-tune the demo based on your specific needs. You’ll find out how easy it can be to secure your sensitive data.

